
Ex-military arrested for gathering intelligence on Ukraine’s air defense systems for Russia
The man was trying to pass classified data to the Russian intelligence agency, having planned a trip to Russia to this end under the pretext of a family visit, the Security Service (SBU) wrote in a statement.
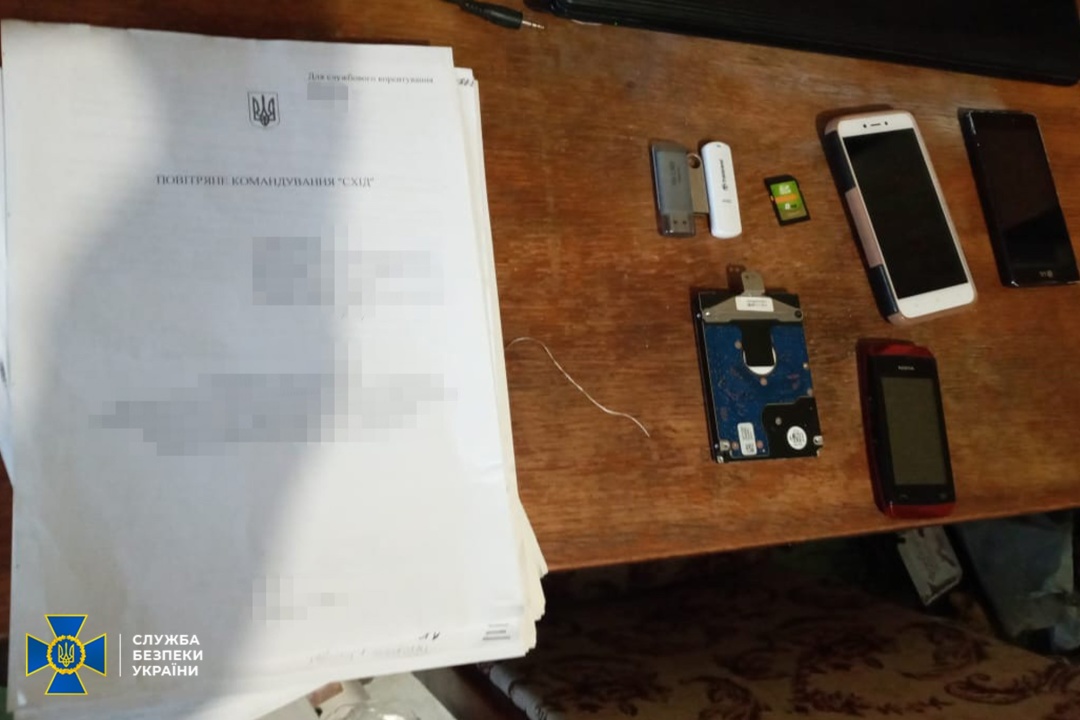
The SBU operatives seized from the culprit the materials he had illegally obtained on the organization of the air defense control system.
The inquiry established that the former serviceman had been secretly collecting sensitive data, including classified information at his base. The perpetrator is believed to have made unauthorized copies of classified defense data by unlawfully interfering in the unit's automated information systems.
The man kept the obtained secrets at home.
During a warranted search in his apartment, law enforcers found flash drives with classified military information on them; computer hardware and communication means with evidence of unlawful activity.
The SBU is set to press formal charges, while the court is yet to select and impose on the suspect a measure of restraint pending further pre-trial inquiry.

The criminal proceeding has been initiated under Part 1 Art. 258-3 (Participation in a terrorist group or terrorist organization) and Part 2 Art. 362 (Unauthorized actions with information processed in computers, automated systems, computer networks or stored on such media, committed by a person with authorized access to it) of the Criminal Code of Ukraine.
The sting operation was run by the SBU Military Counterintelligence Department and the agency’s local unit in Dnipro under the procedural guidance of the local branch of the Specialized Prosecutor's Office for military and defense cases.
As reported earlier, the SBU counterintelligence prevented another attempt to transfer classified defense information to Russian intelligence when a Ukrainian Army unit commander was exposed for secretly collecting military secrets on missile depots across the country.
im




